Dr web cureit june 2 2012
22.02.2018 – Advertisements or commercial links. If the owner of the mobile device agrees to do it, Find and Call collects contact information found in the device and uploads it to a remote server. You are logged in as.
For windows dr web cureit june 2 2012 zimbabwe

What’s New?
1. 5By downloading the free version of Dr. The malware, dubbed by Dr.
2. 3 Statistics showing encoder Trojan-related support requests by country are presented in the diagram below. For a free product this is an exceptionally thorough, easy to use and re-assuring piece of software.http://softik.org/anti-trojan-elite-v5-2-8-patch-rar/For those of you who get blue-screened or their computer gets worse–Gee, maybe they have a serious infection they should have dealt with long back or have a hardware issue.
3. 7 On July 23 Doctor Web’s anti-virus laboratory received a malware sample which turned out to be a multi-purpose backdoor comprising a large number of functional modules such as rootkit drivers used to hide the application in the system. Detections of Trojan downloader modifications have multiplied as well. http://softik.org/ccleaner-for-windows-7-32-bit-filehippo/This information will help Doctor Web analyse in-depth the global anti-virus security situation and perfect the detecting and curing routines incorporated into Dr. To learn more about the Win
Blog Archive

4. 1 It seemed that Mac OS X users worldwide were at least informed about the potential threat, and that one could soon expect the planet to be completely free of infected Macs. Login or create an account to post a review.Dr web cureit june 2 2012One of them is designed to detect virtual machines in an infected system, and the other enables intruders to disable a variety of anti-virus programs, if installed in the system. Also, incidents took place involving Trojans for Android being spread via Google Play:
5. 1 Init was used by intruders to create the largest botnet in history, which included more thaninfected Macs. Dande mostly incorporates computers owned by pharmacies and pharmaceutical companies.
6. 6 By the end of July, the number of infected computers was 2,
7. 1 The diagram below provides a list of Trojan encoder modifications that, according to Doctor Web’s anti-virus laboratory, most frequently infected computers in July.
Para bajar dr web cureit june 2 2012 registry
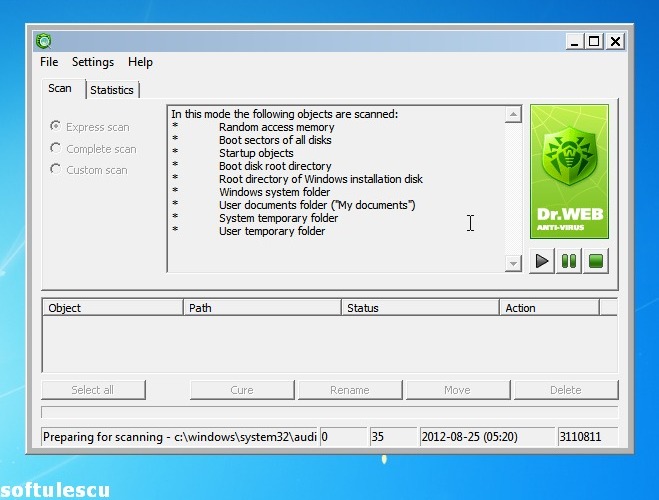
Portable anti-malware tool based on the Dr. WEB engine, which can run express scans to find cureit neutralize threats, featuring a quarantine manager.
Designed to conduct on-demand scans to remove viruses, adware, spyware and rookits, the utility does not ensure round-the-clock PC 2012. Instead, it can run as a secondary shield against e-threats by pairing it with the real-time guard of another av product, since there will be no software conflicts leading to OS stability issues.
Since there is no setup involved, there are two ways to deal with Dr. It can be either saved in any part of the hard disk or stored on a pen drive to directly run regular checkups on other PCs without any installers.
What’s more, the app does not modify Windows registry settings. As far as the interface is concerned, the software utility adopts a simple and elegant look which does not highlight visual elements but rather focuses on functionality.
There is june one scanner type with predefined settings provided by Dr. Users may personalize the scanning behavior when it comes to the target locations and object types e.
For each threat type, the app can make a move defined by the user, like attempting to fix infections or moving them to the quarantine immediately. It is possible to create exclusions, include archives, emails and installation packages in the scan, manage the quarantine, examine log information and indicate the logging level scan details to keep track ofand so on.
Our latest tests have shown that Dr. It may take a very long time to finish scanning, however, excluding the scan configuration and disk size factors. Nevertheless, casual and advanced users alike may resort to Dr.
Part of these download collections: Mar 23rd, Freeware. Russian anti-virus company Doctor Web has updated Dr. Web Anti-rootkit API Web Scanning Engine The update resolves web issue that caused the scanner to freeze if the utility was started using the option ‘Run as’.
Read the full changelog.
2015 dr web cureit june 2 2012 for windows
In particular, such threats include numerous Android. Do you have anti-virus software installed on your computer, but still worry about its effectiveness? For example, in Russia criminals often registered at job search portals as potential employers and promised would-be-workers high salaries to lure them onto a bogus site. Cons The free version sends scanning statistics and system information to Doctor Web, but no personal information. Monthly reviews Real-time threat news About viruses About mobile threats. Threats to Android The rate at which new threats to Android are identified appears to be steady.
Wheels steel dr web cureit june 2 2012 code generator
In addition, in July Trojan. AVKill programs that were actively spreading a month ago have virtually disappeared from mail server malware statistics. The number of bots in the largest botnet BackDoor.
Nevertheless, despite the release of operating system updates, anti-virus software for Mac OS X, and an array of tools to remove BackDoor. The graph below shows how the number of BackDoor.
Over the past month the number of Win We’d like to remind you that Win It was designed to make web injections—that is, it can embed code into loaded web pages. The graph showing changes in the number of Win A similar situation exists concerning the Win It is also growing, though not so rapidly: A graph showing changes in the number of bots is presented below.
Earlier this month, Doctor Web warned users about the growing BackDoor. Dande botnet which targets the activities pharmaceutical companies. This Trojan steals information from client applications used to order pharmaceutical products.
Since the Trojan will operate only on computers running electronic medication order software, we can assume that the botnet BackDoor. Dande mostly incorporates computers owned by pharmacies and pharmaceutical companies.
At the beginning of July , there were 2, infected machines and 2, By the end of July, the number of bots has not changed: On July 23 Doctor Web’s anti-virus laboratory received a malware sample which turned out to be a multi-purpose backdoor comprising a large number of functional modules such as rootkit drivers used to hide the application in the system.
The file determines the OS type and saves and launches an infected application in the compromised system—currently, Doctor Web’s virus analysts have Trojan samples intended for Windows and Mac OS X.
It is known that a version targeting mobile platforms also exists. The malware features a modular architecture: These drivers enable the malicious application to conceal itself.
All Trojan versions use the same configuration file containing the modules’ settings. In addition, the Trojan saves and transmits information about the infected machine to criminals, acts as a key logger, and can take screenshots and intercept e-mail, ICQ, Skype messages and data captured by a microphone or video camera connected to a computer.
In addition, the backdoor has a large set of tools with which to bypass anti-virus software and firewalls, so it may run unnoticed in a system for a long time. During the month, Doctor Web found a number of new malicious programs for Android.
Thus, in early July, Doctor Web’s analysts discovered several malicious applications distributed via Google Play. According to available statistics, these programs have been downloaded by users more than 18 thousand times.
Its main objective is to purchase apps in the store run by China Mobile without user consent. The Trojan performs all steps automatically: The potentially dangerous application Find and Call Program.
Find and Call is marketed as an effective tool for communication. When launched, it prompts a user to undergo an authorization procedure and enter their e-mail address. If the owner of the mobile device agrees to do it, Find and Call collects contact information found in the device and uploads it to a remote server.
The server uses obtained contact information to send SMS messages encouraging recipients to install the application, whereas the user who installed the program is designated as the sender.
In addition, several signatures for new modifications of Android. SmsSend were added to the virus databases. This application is distributed as an attachment to spam messages including those supposedly sent by DHL.
It poses a threat to users of e-banking services RBS , because it allows attackers to steal confidential information by intercepting data submitted through forms in the browser window and by embedding its code into bank web pages.
More information about this threat can be obtained from the material published by Doctor Web. At the end of the month, a mass spam mailing was registered in the social network Twitter.
Messages were written in Russian and included a link which, depending on what browser was involved, could direct a user to a fraudulent site or a resource from which malware for mobile devices can be downloaded.
In addition, the second half of July saw the emergence of the Trojan downloader known as Trojan. It has a wide set of tools for identifying debugging and analysis software and, moreover, can access NTFS via its own routine rather than Windows API which is rather uncommon for this type of malware.
To get your award points, go to the news page when logged in under your Doctor Web account or create an account. Your account must be linked with one of your social network accounts in order for you to receive award points for participating in our website activities.
What is the benefit of having an account? The overall strength of the botnet, consisting of computers carrying the file infector Win By the end of July, the number of infected computers was 2, At the same time, the influx of new joiners virtually stopped.
The average daily number of new bots connecting to the command and control server is not exceeding The number of machines on which Dr. Web software detects malware dubbed Trojan.
In early July it diminished to 7, discovered malicious samples and, by month’s end, it dropped to 4, with no more than 40 newly infected hosts appearing on the network daily.
The decline in the number of Trojan. The number of nodes in the botnet created with BackDoor. This malignant application is designed to carry out spam mailings. In July, its botnet contained an average of 2, active bots daily, with newly infected hosts contacting the BackDoor.
The growth in number of hosts infected with BackDoor. The botnet’s activity is illustrated in the graph below. These figures suggest that the botnet BackDoor. The main reason behind such persistence is carelessness on the part of Mac OS X users.
The remarkable regularity with which the Dr. Web virus database is acquiring new entries for a variety of mobile device commercial spyware once again proves the fact that such services are not only in demand, but also increasing in popularity in today’s high-tech market.
Last month, Doctor Web’s analysts found a large number of new versions of known spyware programs such as Android. Mobimon , as well as the new families Program. Such applications enable intruders to monitor various user activities and are often available for several mobile platforms including Android, BlackBerry and Symbian OS.
While the stock of commercial software for monitoring, which can be used both legally and in violation of the law, is increasing, purely cybercrime-related services designed to obtain sensitive information from mobile devices are becoming mass market too.
Special programs that enable criminals to embed Trojan features in any Android application serve as a good example. Raziel are two such “products” discovered by Doctor Web’s analysts.
The first utility uses for its operation the source code of AndroRat, a freely distributed program for remote access and administration, which has been known since and is detected by Dr.
In the second case, the utility’s author makes use of their own Trojan spy program, which can either be built into an Android app or compiled into a separate apk-package. This malware has been added to the virus database as Android.
Such utilities are relatively easy to use and enable people with low programming skills to create Trojans for Android. The number of such toolkits is likely to increase in the near future.
In the second month of summer, Android also saw the discovery of several vulnerabilities, with Master Key being among the most notable. The flaw in Android security routines enabled installation of unsigned applications from packages containing files with identical names.
Thanks to prompt action on the part of Doctor Web’s virus analysts, routines to detect the applications that exploited this vulnerability were implemented in the Dr. Web for Android anti-virus: The first Trojan to exploit this software flaw was discovered less than a month after information about the vulnerability Master Key appeared in the public domain.
The malware, dubbed by Dr. This Trojan is able to send SMS messages, intercept incoming messages, and send confidential information such as the phone number, as well as information from the phone book of the compromised device, to a remote server.
For more information about this threat, please refer to the review published on our website. And some threats came from Google Play.


