Dr web security space 8 0 0 11100 final

17.02.2018 – How do you ensure the privacy of my data in the cloud? Is your cloud in compliance? Their experienced and friendly engineers will provide the knowledge needed to get the most out of your data center environment and personnel.
Zip dr web security space 8 0 0 11100 final you stick
What’s New?
1. 9Web Anti-virus for macOS.
2. 3 Pure Storage has cracked the code and destroyed the disk status quo. Enjoy a cup of coffee while catching up with your IT-professional peers and visiting with our vendors, before beginning your day of education and networking.http://softik.org/zd-soft-screen-recorder-4-1-3-0-team-rjaa/For many CIOs and IT managers, the benefits of moving to the cloud—increased efficiency, reduced cost, excellent scalability, pay-as-you-go pricing, the latest technology without the capital expense—are offset by concerns about security and service quality. The Chapter promotes an organized forum for continuing education and exchange of ideas amongst its members to improve healthcare information and management systems that support patient care and wellness.
3. 2 Before joining Veeam he served as a senior systems engineer for a Tacoma based medical imaging company. http://softik.org/autorun-virus-remover-v3-0-build-0201-cracked-zaejp/Silver Peak software accelerates data mobility between data centers, branch offices and the cloud, which helps your company: With his help it is also possible to forbid the use of portable devices for storage of data, to lock access to the networkings issues, and also separate files and catalogues and protect important information ot a delete or theft.
Welcome to the Torrof!

4. 7 When you need someone to help you manage your archiving migration and electronic discovery needs, you need a company you can count on, with knowledge, experience and integrity to get it right the first time. How fast will we be back up and running after a disaster?Dr web security space 8 0 0 11100 finalADTRAN solutions are currently in use by service providers, private enterprises, government organizations and millions of individual users worldwide.
5. 6 We envision our community as collaborative, vibrant, entrepreneurial, and connected – where technology is a tool which contributes to prosperity for our people and organizations. It is our goal, our purpose to provide a community network for the IT business professionals to reach their true potential by providing education programs for advancing technology and business skills, leadership development opportunities, networking, peer mentoring and knowledge sharing, and online resources.
6. 3 Download a free three-month trial For Windows Dr. Known for its progressive programs, workshops and symposiums, the organization has become a unifying force in defining and leading the continuously evolving fields of business continuity, disaster recovery, and emergency response the “profession”.
7. 6 Detection of viruses using rootkit technologies. Award-winning Saleslogix enables intelligent collaboration and best practice automation across sales, marketing, and service — recommending and performing winning actions to help drive revenue and an exceptional customer experience.
Dr web security space 8 0 0 11100 final for
Now the search for and neutralization of complex threats rootkits, bootkits, etc. The resident background scan routines search for active threats among critical system objects and in the BIOS.
An intelligent assessment of hardware capabilities ensures that scanning does not interfere with the user experience. The integration of the installation package installer with the updated anti-rootkit makes it possible to repel active threats and cure a PC during installation, even if the computer is infected with sophisticated malware.
Web can block automatic modifications of critical Windows objects, thus ensuring preventive protection from infection. For various applications and services, a user can grant or deny access to certain Windows objects in real time and foil attempts by malware to make unwanted changes in a system.
The new service Dr. It helps prevent infection even from malicious sites that have not yet been added to the Dr. When an attempt is made to go to an infected website, the URL is sent to the Doctor Web server for examination in real time.
It is now possible to customize parental control settings individually for each computer user. Internet and PC usage time can also be set for each profile separately. The Parental Control also makes it possible to block access to devices and peripherals such as flash drives, printers, external hard disks, and USB devices which allows sensitive data to be protected from unauthorized access, copying, or deletion.
A single control center for all the components except the scanner is another innovation of Dr. Download All New Software. Share this post Tweet. Outpost Security Suite Pro 8. AVG Internet Security AllMyNotes Organizer Deluxe 3.
Evaer Video Recorder for Skype 1. IObit Protected Folder 1. About Me Natasha Lilly. About – Privacy Policy – Contact us.
Dr web security space 8 0 0 11100 final windows
The prizes are different at every conference, but in the past have included items such as iPods, golf clubs, sporting event tickets, and eReaders. We take pride in giving you the software solutions, data flow and knowledge to run your back office with maximum efficiency. Virtualization, high performance workloads, smaller budgets, lower recovery point objective, and shrinking backup windows have changed the requirements of data protection that are forcing many companies to rethink strategies. ISACA members’ participations in running the chapter are highly encouraged. No more wondering how much data you can analyze, how fast you can respond to a customer, or how quickly you can launch a new service.
Free update dr web security space 8 0 0 11100 final update
Internet and PC usage time can also be set for each profile separately. The Parental Control also makes it possible to block access to devices and peripherals such as flash drives, printers, external hard disks, and USB devices which allows sensitive data to be protected from unauthorized access, copying, or deletion.
A single control center for all the components except the scanner is another innovation of Dr. Download All New Software. Share this post Tweet. Outpost Security Suite Pro 8.
AVG Internet Security The page may not load correctly. Web AV-Desk service providers curenet. Buy from our partners Buy online Ask about a purchase. Send a message A query form.
For other OSs Dr. Use free of charge. Via bank and payment systems. Via cellular service providers. Via IT service suppliers. Download a free three-month trial For Windows Dr. For other OSs macOS.
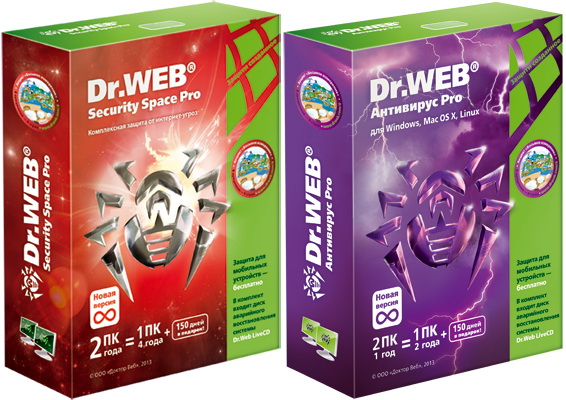
Protection for mobile devices Android. New license Renew Expand. Documentation FAQ Product videos. Register serial number Download software Self-support. Web Security Space protection components Operating system Windows macOS Linux Anti-virus Blocks viruses and malware from accessing the protected system and will cure the malignant programs that have already penetrated it.
Bonus Users of this product receive our gift—free protection for Android! Loyalty programme for regular Dr. How can I earn Dr. The WCTA produces events designed to enhance business networks and to inform and educate its membership, policymakers and citizens.
We work with members to provide expert sources for the media, policy makers, and investors. Our events, communications, and contacts are designed to constantly put members together with the collaborators, investors, government officials, customers, and vendor that help them grow and be successful.
West Sound Technology Association WSTA is a non-profit, tax exempt c 3 educational organization dedicated to increasing public awareness of issues affecting technology professionals and the industry, improving education and business success through the effective integration of technology, increasing skills and the availability of workforce opportunities, and enhancing cooperation between business, community, governmental, and educational stakeholders to drive a technology future for the West Puget Sound.
The mission of WSTA is to educate, influence and promote an innovative and vital technology economy. We envision our community as collaborative, vibrant, entrepreneurial, and connected – where technology is a tool which contributes to prosperity for our people and organizations.
As one of the oldest and largest statewide technology trade associations in North America, we’re passionate about promoting Washington as a desirable place to start and grow successful technology companies amid a strong and connected community.
WTIA is the place to connect to Washington’s technology industry. Zones is proud to offer a carefully chosen mix of products, solutions and services to help their clients meet IT goals and business objectives.
Zones simplifies information technology. Their expertise carries over to Zones lifecycle management services such as technology assessments, data center engineering, virtualization and cloud computing planning, and software asset management.
Please see the summary below, and check back later to review the agenda and other details of our event. Join your peers at the conclusion of the conference to enjoy the Executive Reception.
The first guests will receive a complimentary glass of beer or wine. Continuing professional development or continuing professional education is the means by which people maintain their knowledge and skills related to their professional lives.
Make sure to check the appropriate box when completing your registration, or contact us here. The Showcase will feature the latest clean tech innovations from Northwest companies and research institutions.
Expert speakers and break-out sessions will further highlight over 20 companies focused on sustainability and new technologies. Enjoy table-top presentations, poster sessions and business development opportunities.
Full-day registration includes breakfast, lunch and reception. Read Biography Presentation Synopsis Must be present to win. Enjoy a cup of coffee while catching up with your IT-professional peers and visiting with our vendors, before beginning your day of education and networking.
Brett is responsible for developing the bank’s IT and facilities strategies and maintaining the bank’s technology and facilities infrastructures. He has over 23 years of experience implementing and supporting numerous technologies for several industries including military, aviation, engineering, manufacturing, and mechanical contracting.
His full resume can be viewed at www. In light of the recent retail data breaches such as Target, Michaels, and Neiman Marcus, what are the information security, banking, and retail industries doing to protect consumers?
Is there an information security “silver bullet”? On October 26, , President Bush signed into law H. The concept of the ECTF network is to bring together not only federal, state and local law enforcement, but also prosecutors, private industry and academia.
The common purpose is the prevention, detection, mitigation and aggressive investigation of attacks on the nation’s financial and critical infrastructures. The ECTF meeting will be very fluid, focusing on local trends in cyber-crime such as credit card skimming, point of sale system breaches and an expanded discussion on steps businesses can take to prevent such breaches.
Steve is currently the Director of Information Technology for Metropolitan Market an award winning grocery store spanning across Seattle and Tacoma. Previously he was the Director of Corporate Business and Information Technology for Uwajimaya a progressive Asian Supermarket located in the pacific northwest since His experience with Uwajimaya spans across 26 years which involves being a part of the executive leadership team and 17 years leading Uwajimaya’s Corporate Business and Information Technology initiatives.
This presentation will share insight and perspectives on leading and managing the business and information technology initiatives that tap into how leadership, adapting to constant change and supporting a business through the collective process of fortifying your people, process and technology.
Join Grant Asplund, Sr. Technology Evangelist for an entertaining and informative look at the Advanced Threat Lifecycle Defense. Learn how to align your business processes around new web security intelligence and technologies to fortify your security infrastructure against future attacks.
Find out how this approach will empower your digital enterprise and organization, enabling you to adopt the best new technologies that drive your business. He has over 6 years of experience as a systems engineer with a experience in virtualization, networking and storage.
Before joining Veeam he served as a senior systems engineer for a Tacoma based medical imaging company. IT organizations of all sizes have embraced server virtualization as a way to reduce costs and enhance service delivery.
Our customers understand that virtual environments bring unique challenges. Our powerful, easy-to-use and affordable solutions help solve virtualization challenges — making Veeam the perfect fit for the modern datacenter.
He has over 20 years of diverse technology industry experience including leadership roles in software development, IT management consulting, business development, and product marketing for companies such as IBM, Accenture, Sun, and Cisco prior to joining EVault.
For many CIOs and IT managers, the benefits of moving to the cloud—increased efficiency, reduced cost, excellent scalability, pay-as-you-go pricing, the latest technology without the capital expense—are offset by concerns about security and service quality.
While all methods of data storage involve some risk, you can minimize that risk by choosing a provider with strong, comprehensive principles for security, data protection, and disaster recovery.
How do you do that? How do you ensure the privacy of my data in the cloud? How do you handle the security of access to your cloud? Is your cloud in compliance? How fast will we be back up and running after a disaster?
Will you be there when we need you? Asking a few targeted questions now could save you from facing many more hard questions later. Start by joining EVault Senior Product Marketing Manager, Shawn Swanson, who will help you determine what key questions to ask your cloud provider and the answers you should expect.
Calderon has lead numerous efforts in marketing, educating, assessing, designing, deploying, and operating of solutions for Manufactures, Systems Integrators and End User Customers in the Government and Commercial sectors.
Before embarking on any Cloud journey for an application it’s imperative to understand all of the interrelated components that constitute an application stack. The role is accountable to: Security and IT Optimization are primary concerns for most organizations seeking to identify threats risk, reduce risk and increase operational efficiency in order to achieve a competitive advantage.
LaaS is a model for centrally ingesting and collecting any type of log files coming from any given source or location. Prior to Bluesocket, Chris was the Vice President of Sales and Marketing at Datacom Systems, a leading technology company focused on data capture infrastructure.
User expectation around Wi-Fi in the enterprise is changing dramatically. Fueled by consumerization, BYOD, and new standards such as Recent developments in cloud control and network virtualization are opening up a whole new approach to the deployment of Wi-Fi.
Chris has worked at IVOXY for 4 years assisting many customers with virtualization design, implementation, and integration. Prior to IVOXY, Chris worked in a number of engineering roles at companies in the construction, retail, and investment industries.
Additionally, Chris is an instructor at IVOVXY consulting, teaching on subjects ranging from vSphere advanced performance tuning, to disaster recovery design. Protecting the datacenter can be complex and costly challenge for modern information technology departments.
Virtualization, high performance workloads, smaller budgets, lower recovery point objective, and shrinking backup windows have changed the requirements of data protection that are forcing many companies to rethink strategies.
Join us for a discussion and reference design that will introduce data protection concepts in a modern, high performance datacenter. Special Agent David Mills U.
This model has worked well for us and we offer it only as a model for your consideration. The process of combating cyber-crime is changing daily as technology and knowledge of the subject changes.
The ECTF model is flexible and scalable and is very basic and simple. It relies on communication and the development of relationships to be successful. For the past 11 years Mr. Johnson has held the position of Chief Information Security and Privacy Officer in which he oversees information security and privacy issues for the entire county.
In this capacity he established the information assurance program from policy development to controls selection, implementation, monitoring and evaluation. Since December Mr. He holds multiple certifications in information security, information privacy, network administration and project management.
This presentation will cover the concept of critical infrastructure and the 16 identified sectors. Johnson will explain why protecting the information systems and infrastructure that support critical infrastructure is important.
Today, through mobility, ad-hoc teams can use online tools to work together from anywhere in the world. In the future, location will not matter, traditional offices will be obsolete, and virtual teams will work across time, space, and organizational boundaries using collaborative tools.
Mobility is a key strategy for any organization hoping to keep pace with our changing times. King County has developed a mobility strategy for now, and into the future.


